Unmasking the Deep State: Cold War Subversion, the P2 Lodge, and Modern Whistleblowers
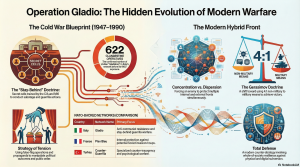
April 1, 2026 /Mpelembe Media/ — The historical sources detail the emergence of a covert “shadow government” architecture that originated during the Cold War. Initially organized by NATO, the CIA, and MI6 as clandestine “stay-behind” armies (such as Operation Gladio) to mount armed resistance in the event of a Soviet invasion, these networks frequently evolved into instruments of domestic political subversion. Across Western Europe and Turkey, right-wing paramilitary units employed a “strategy of tension,” staging false-flag terrorist attacks to spread public fear, discredit left-wing political movements, and justify authoritarian crackdowns. Prominent examples of this state-sponsored terror include the 1969 Piazza Fontana and 1980 Bologna massacres in Italy, as well as the Brabant massacres in Belgium.
In Italy, this systemic destabilization was heavily coordinated by the Propaganda Due (P2) Masonic lodge, which functioned as a “state within a state”. Under the leadership of Licio Gelli, P2 infiltrated the highest levels of the Italian military, intelligence services, and media to implement a “Plan for Democratic Rebirth”. This subversive program was designed to reshape Italy into an authoritarian democracy through widespread political corruption, the suppression of labor unions, and control over the press.
The consequences of prioritizing covert operations over democratic transparency extend into modern geopolitics through “blowback” from unchecked intelligence programs. Former US consular officer J. Michael Springmann revealed how he was pressured to issue US visas to unqualified recruits for the Soviet-Afghan war—CIA-backed Muslim operatives who later formed Al-Qaeda. Similarly, former FBI translator Sibel Edmonds exposed a massive post-9/11 corruption ring involving US officials illegally selling nuclear technology and intelligence to foreign operatives. Her attempts to expose these national security threats were subsequently silenced by the Justice Department’s invocation of the “state secrets privilege”.
Today, the tactics pioneered by these stay-behind networks are recognized as early blueprints for modern hybrid warfare. Blending conventional military force with irregular methods like disinformation, cyber warfare, and proxy terrorism, hybrid warfare aims to destabilize target nations from within without triggering formal, declared war. To counter these complex covert threats, vulnerable states are increasingly adopting “Total Defense” strategies, a whole-of-society approach that incorporates civil, economic, and psychological mobilization to make populations highly resilient against foreign subversion.
The Skeleton in NATO’s Closet: The Clandestine Ghost Armies of the Cold War
While the world’s attention was fixed on the “Iron Curtain” and the visible military posturing of the Cold War, a clandestine history was unfolding beneath the feet of Western Europeans. Operating in the shadows was a secret network of “stay-behind” armies—dormant cells designed to serve as a resistance force in the event of a Soviet invasion. These networks were intended to be the final line of defense, trained to conduct sabotage and guerrilla warfare on their own national soil if occupied by the USSR.As an investigative historian, one must look past the official narratives of “readiness” to find the inherent tension of the era: a strategic necessity that frequently collided with democratic sovereignty. These networks were not born in a vacuum; their DNA can be traced back to 1940 and Winston Churchill’s creation of the Special Operations Executive (SOE), tasked to “set Europe ablaze.” Following the war, this “SOE model” was adapted by the CIA and MI6 to ensure that if the red tide ever swept across the Continent, a ghost army would be ready to haunt the occupiers.
The Hidden Infrastructure: Weapons in Caskets and Churches
The logistical scale of these networks was immense, blending military precision with the macabre. In Italy, the stay-behind network—codenamed Gladio—utilized a sophisticated infrastructure of hidden weapon stockpiles known as “Nasco” caches. Between 1959 and 1960, the CIA supplied the majority of the equipment for these caches, which included powerful explosives like C4, grenades, and handguns.These materials were hidden in more than 100 locations across the Italian peninsula, specifically chosen to evade discovery. Caches were buried in forests, fields, and—providing a chillingly literal meaning to “dead drops”—inside caskets in cemeteries and beneath church grounds. The network was composed of 622 civilian volunteers, meticulously vetted for their anti-communist credentials and trained at the Centro Addestramento Guastatori (CAG) at Capo Marrargiu in Sardinia.The existence of this secret infrastructure only came to light in 1990 when Italian Prime Minister Giulio Andreotti made a startling revelation to the parliament.”Andreotti defined Gladio as a covert resistance network whose primary objectives were intelligence collection as well as sabotage, propaganda, and guerilla warfare, all to be activated in case of an enemy’s invasion.”
The “Strategy of Tension”: When Defense Becomes Subversion
For the geopolitical strategist, the most troubling aspect of these networks is the shift from defensive preparedness to domestic political subversion. This evolution birthed the “Strategy of Tension,” where clandestine actors sought to influence the political equilibrium of Western nations through “false flag” operations intended to terrorize the public into accepting authoritarian stability.A primary example is the 1972 Peteano attack in Italy, where a car bomb killed three Carabinieri. While investigators initially blamed left-wing extremists, the detonator for the C4 was eventually traced back to a specific “Nasco” cache found in the Friuli region. Vincenzo Vinciguerra, a member of the neofascist organization Ordine Nuovo , later confessed to the crime. He revealed that neofascist actors utilized Gladio-supplied materials to frame the left, aiming to provoke a law-and-order crackdown.This era of subversion is inextricably linked to the controversy surrounding the “Westmoreland Manual” (Field Manual 30-31B). Purportedly signed by General William Westmoreland, the manual instructed U.S. forces to carry out acts of violence in allied countries to be blamed on communist subversives. While many experts point to style and formatting errors to argue the document was a Soviet forgery designed to alienate NATO allies, the strategist must ask: does the manual’s likely status as a forgery matter if the actions it described were actually occurring on the ground?
The Shadow Government: Licio Gelli and the P2 Lodge
At the heart of Italy’s clandestine political landscape was Licio Gelli, the “Puppet Master.” Gelli was the Venerable Master of the Propaganda Due (P2) masonic lodge, a clandestine group that functioned as a shadow government.In 1981, a police raid on Gelli’s villa in Arezzo led to the discovery of a membership list containing 962 names. This list was a “who’s who” of the Italian establishment, including the heads of all three secret services and future political leaders like Silvio Berlusconi. Gelli’s influence was not merely domestic; he was a global broker of influence, leveraging his ties to the military junta in Argentina (where he held the Gran Cruz de la Orden del Libertador ) to facilitate complex three-way oil and arms deals between Libya, Italy, and Argentina. Gelli represented the ultimate failure of clandestine networks: a secret army that had turned its weapons toward the halls of power.
Not Just Italy: The Pan-European Scope
While Gladio is the most notorious, stay-behind networks were established across nearly every NATO member state, coordinated through NATO’s Allied Clandestine Committee (ACC) and the Clandestine Planning Committee (CPC).
France: Often framed as a standard network, “Plan Bleu” was actually exposed in 1947 by Interior Minister Edouard Depreux as a right-wing conspiracy to carry out a coup d’état against the Republic. A subsequent network, “Mission 48,” focused on neutralizing communist subversives and planning for a government-in-exile in North Africa.
Turkey: The “Counter-Guerilla” branch, overseen by the Special Warfare Department, was linked to the 1977 Taksim Square massacre. Most notably, the generals who led the US-backed 1980 military coup were themselves the leaders of Turkey’s stay-behind branch.
Denmark & Belgium: Denmark operated the “Absalon” network, while Belgium utilized the SDRA8 (military) and STC/Mob (civilian) branches. In Belgium, civilian operatives were strategically placed in society to gather intelligence for a government-in-exile.
The Evolution: From Gladio to “Total Defense”
As highlighted in recent scholarship—including the 2024 work by Matteo Fiorino—the stay-behind principles of the Cold War are the direct ancestors of modern hybrid warfare. However, a fascinating strategic paradox has emerged in the 21st century.In the West, what was once a “secret illegal cell” has been “socialized” into the public doctrine of “Total Defense.” Countries like Finland and Switzerland now utilize a transparent, “whole-of-society” approach to resilience, involving citizens and the private sector in defending against cyberattacks and misinformation.Conversely, modern adversaries have “weaponized” the old stay-behind playbook for offensive use. The Russian “Gerasimov Doctrine” emphasizes non-linear warfare—using informational campaigns and internal destabilization to achieve strategic goals without a formal declaration of war. What NATO once used to protect its rear is now being used to fracture its front.
Conclusion: A Legacy of Ambiguity
The history of NATO’s secret armies remains a complex chapter in European democracy. Born from a legitimate fear of foreign invasion, these networks frequently crossed the line into domestic subversion, impacting the very nations they were sworn to protect. They serve as a permanent reminder of the tension between the perceived requirements of national security and the necessity of democratic transparency.As we navigate an era of hybrid threats, a fundamental question remains: In the pursuit of security, can a secret army ever truly remain dormant, or is the infrastructure of clandestine resistance inherently destined to interfere with the democracy it claims to defend?