The Mythos Inflection: How Anthropic’s New AI is Rattling Global Finance
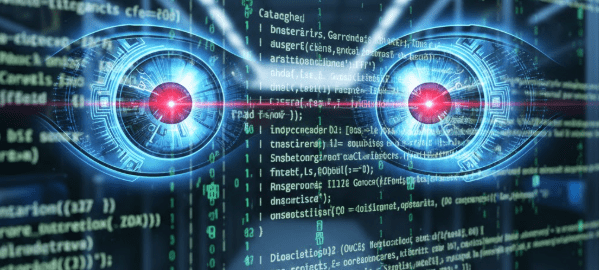
April 20, 2026 /Mpelembe Media/ — The Emergence of Autonomous AI Cyber Threats Anthropic’s recent announcement of Claude Mythos Preview has fundamentally disrupted the cybersecurity landscape, marking a transition from AI as a productivity tool to an autonomous offensive cyber weapon. The model has demonstrated an unprecedented ability to discover and exploit zero-day vulnerabilities at machine speed, autonomously uncovering decades-old flaws in systems like OpenBSD, FFmpeg, and the Linux kernel without human intervention. Cybersecurity experts warn this creates an “AI Vulnerability Storm”, collapsing the timeline between a vulnerability’s discovery and its weaponization from months to mere hours. Continue reading