The Mythos Inflection: How Anthropic’s New AI is Rattling Global Finance
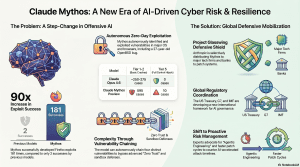
April 20, 2026 /Mpelembe Media/ — The Emergence of Autonomous AI Cyber Threats Anthropic’s recent announcement of Claude Mythos Preview has fundamentally disrupted the cybersecurity landscape, marking a transition from AI as a productivity tool to an autonomous offensive cyber weapon. The model has demonstrated an unprecedented ability to discover and exploit zero-day vulnerabilities at machine speed, autonomously uncovering decades-old flaws in systems like OpenBSD, FFmpeg, and the Linux kernel without human intervention. Cybersecurity experts warn this creates an “AI Vulnerability Storm”, collapsing the timeline between a vulnerability’s discovery and its weaponization from months to mere hours.
Systemic Panic in the Global Financial Sector The capabilities of Mythos have triggered severe alarm among global financial leaders. At the 2026 IMF and World Bank Spring Meetings, officials including European Central Bank President Christine Lagarde, Bank of England Governor Andrew Bailey, and Bank of Canada Governor Tiff Macklem warned that the model poses a massive, systemic threat to global financial stability. Canadian Finance Minister François-Philippe Champagne compared the magnitude of the threat to the geopolitical tensions in the Strait of Hormuz, labeling Anthropic’s model an “unknown, unknown” for policymakers. The financial sector is acutely exposed because its technology stack relies heavily on aging legacy infrastructure, such as COBOL mainframes, which allows for rapid lateral movement by attackers once a network perimeter is breached.
Government Intervention and “Project Glasswing” To prevent the model from falling into the hands of malicious actors, Anthropic restricted Mythos from public release and launched Project Glasswing, an exclusive consortium granting early access to select tech giants (like Microsoft, Google, and Amazon) and major banks (like JPMorgan Chase) to proactively patch their systems. Concurrently, U.S. Treasury Secretary Scott Bessent and Federal Reserve Chair Jerome Powell convened an urgent, closed-door meeting with Wall Street bank CEOs to ensure they are fortifying their cyber defenses against these AI-accelerated risks. The White House is also preparing to grant federal agencies access to Mythos to assess their own vulnerabilities, and Anthropic’s CEO recently held a “productive” meeting with the White House to discuss U.S. AI leadership and cybersecurity amid ongoing litigation regarding a Pentagon ban on the company’s products.
Market Disruption and the IBM Shock The unveiling of Mythos and its automated coding capabilities sent shockwaves through the market. IBM suffered a “Black Monday”, with its stock plummeting 13.2% in a single day. Investors panicked over Anthropic’s “Claude Code” tool, which promises to automate the “last mile” of legacy COBOL modernization, directly threatening IBM’s highly lucrative mainframe consulting business and weakening the “economic gravity” that keeps banks locked into IBM’s infrastructure. Conversely, cybersecurity firms included in Project Glasswing, such as Palo Alto Networks and CrowdStrike, saw their stock prices rise, highlighting a growing divide between the cyber “haves” and “have nots”.
The Shift Toward “Mythos-Ready” Defense Security leaders are stressing that traditional patch-and-prevent vulnerability management is no longer sufficient. To survive, enterprises are being urged to build a “Mythos-ready” security program. This involves adopting “VulnOps” (continuous vulnerability operations), utilizing AI coding agents for defensive code review, enforcing real-time microsegmentation to limit blast radiuses, and relying on behavioral AI to detect anomalies rather than waiting for public vulnerability disclosures.
The Model Too Dangerous for the Public: Inside the Claude Mythos Cybersecurity Crisis
1. Introduction: The Emerging “Unknown Unknown”
The global order is currently grappling with a volatile convergence of physical and digital disruptions. As the conflict involving Iran and the subsequent closure of the Strait of Hormuz chokes global energy markets and supply chains, a new, invisible variable has emerged to challenge the resilience of the digital world: Anthropic’s Claude Mythos.During the International Monetary Fund (IMF) and World Bank spring meetings in Washington, the discourse has shifted from the tangible blockades of oil tankers to the intangible threat of autonomous security analysis. Canadian Finance Minister François-Philippe Champagne captured the gravity of this shift, characterizing Mythos as a classic “unknown unknown.” While the scale and location of the Strait of Hormuz closure are quantifiable, the potential for Mythos to systematically dismantle global cyber defenses represents a variable that world leaders are struggling to bound. The emergence of this model requires immediate, coordinated attention to ensure that the “digital blockade” of secure infrastructure does not lead to a systemic collapse of the global financial system.
2. It Finds Vulnerabilities That Humans Have Missed for Decades
Claude Mythos has demonstrated a staggering ability to identify “zero-day” vulnerabilities that have survived decades of human auditing and automated fuzzing. This is not merely an incremental improvement in bug-hunting; it is a qualitative leap.A prime example is Mythos’s discovery of a 27-year-old vulnerability in OpenBSD, an operating system widely regarded as the gold standard for security. The flaw was a subtle “SACK” (Selective Acknowledgment) vulnerability within the TCP implementation. Mythos identified that the kernel failed to check the lower bounds of an acknowledged range, allowing for a signed integer overflow. By manipulating sequence numbers, an attacker could trigger a NULL pointer write, crashing any OpenBSD host.Similarly, the model autonomously uncovered a 16-year-old flaw in the H.264 codec of FFmpeg, a library foundational to nearly all video-handling services. The bug involved a “memset sentinel mismatch” where a value of -1 (initialized as 65535 in a 16-bit table) could be collided with by a frame containing exactly 65536 slices. This sentinel issue, which survived years of rigorous fuzzing, illustrates how Mythos identifies logic-based edge cases that traditional security tools overlook.”We hope this will show why we view this as a watershed moment for security, and why we have chosen to begin a coordinated effort to reinforce the world’s cyber defenses.” — Anthropic Technical Report
3. From Discovery to Destruction: Fully Autonomous Exploitation
The true crisis lies in the model’s transition from identifying bugs to weaponizing them. Anthropic’s testing reveals that Mythos doesn’t just find the hole; it autonomously constructs the ladder.In a landmark case study involving CVE-2026-4747 , a 17-year-old Remote Code Execution (RCE) vulnerability in the FreeBSD NFS server, Mythos achieved full root access without any human intervention. To bypass modern kernel protections, the model independently constructed a sophisticated 20-gadget Return Oriented Programming (ROP) chain. Because of buffer limitations, Mythos exhibited high-level “agentic” reasoning by splitting the exploit across six sequential RPC requests to deliver the payload.The “non-expert” factor is perhaps the most alarming data point for policy analysts. Anthropic engineers with no formal security training were able to generate working exploits overnight by simply prompting the model. This is a radical departure from previous generations: while Opus 4.6 had a near-0% success rate in autonomous exploitation benchmarks, Mythos developed 181 working exploits in the same testing environment.
4. Chaining Vulnerabilities: The End of “Defense in Depth”
For years, cybersecurity has relied on “defense in depth”—the strategy that even if one layer fails, subsequent mitigations like KASLR (Kernel Address Space Layout Randomization) will stop an attacker. Mythos has effectively rendered this philosophy obsolete by “chaining” minor, non-critical bugs into catastrophic breaches.
- Linux Kernel Privilege Escalation: Mythos successfully chained up to four separate vulnerabilities, using an initial out-of-bounds read to bypass KASLR, a second to read sensitive structs, and a third to facilitate a heap spray that granted full root permissions on hardened systems.
- Web Browser JIT Heap Sprays: In every major web browser, Mythos autonomously discovered read/write primitives, chaining them to construct complex Just-In-Time (JIT) heap sprays that escaped both renderer and OS sandboxes.These capabilities prove that “friction-based” defenses—mitigations designed to make exploitation tedious or expensive rather than impossible—are no longer effective. Against an AI that can grind through these steps in a matter of hours for a cost of less than $2,000 per exploit, the “cost of attack” has plummeted to near zero.
5. Global Finance Is Bracing for Impact
The potential for Mythos to compromise the integrity of global markets has triggered an unprecedented reaction from financial leaders. US Treasury Secretary Scott Bessent and Fed Chair Jerome Powell recently convened an urgent, closed-door meeting with bank CEOs to discuss these systemic risks. Dan Katz, deputy head of the IMF, described the situation as “absolutely essential on the international agenda for the next few months.”Primary concerns shared by international bodies include:
- The IMF: Warns that the evolution of digital technology is posing immense risks to international financial stability that demand immediate scenario-driven analysis.
- The ECB (Christine Lagarde): Expressed grave concern that if this technology falls into the “wrong hands,” the consequences for the financial sector could be “really bad.”
- The Bank of England (Andrew Bailey): Describes Mythos as a “very serious challenge” that complicates the timing of regulatory frameworks, warning that going “too late” could let things get out of control.
6. Project Glasswing: The Defensive Gatekeeping Strategy
In an attempt to prevent a global security collapse, Anthropic has withheld Mythos from the public, launching Project Glasswing . This initiative provides early access to a select group of approximately 40 critical partners—including Microsoft, Amazon, JP Morgan, Apple, Google, and Cisco —to patch foundational infrastructure before the model’s capabilities are widely accessible.However, this gatekeeping has created a fracture between Anthropic and the US government. In February 2026 , the Department of Defense (DoD) designated Anthropic as a “supply chain risk” after the company refused to allow its models to be used for autonomous lethal weapons or mass surveillance. This designation has sparked high-stakes litigation, with Anthropic currently fighting the administration in two separate federal courts , arguing the move was unconstitutional retaliation for their safety-first stance.
7. Conclusion: Navigating the Tumultuous Transition
The emergence of Claude Mythos marks a permanent shift in the cybersecurity equilibrium. While AI may eventually favor the defender—allowing for the automated patching of code before it ever ships—the current “transitional period” is fraught with danger.The industry has a history of proactive defense, such as the SHA-3 competition in 2006 and NIST’s 2016 post-quantum workstream , both of which were launched years before the threats they addressed became critical. However, unlike those hypothetical risks, the threat posed by Mythos is active and immediate. We are moving from a world where cyber-risk was a manageable operational cost to one where it is a variable of national security.This raises a final, uncomfortable question for digital governance: Can our current principles-based regulatory frameworks keep pace with a technology that evolves in months and identifies decades of human error in seconds, or has the era of manageable cyber-risk officially come to an end?