Category Archives: Security
Standards vs. Policies: Crafting Your Organization’s Cloud Security Framework
Why Your Cloud is More Vulnerable Than You Think
The Spanish AI Loophole That Hacked Mexico
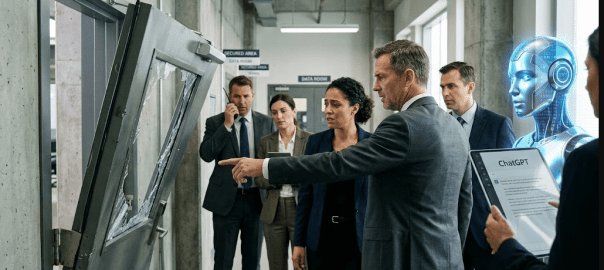
Hacker Weaponizes AI Chatbots to Steal Massive 150-Gigabyte Data Trove from Mexican Government
28 Feb. 2026 /Mpelembe Media/ — An unknown hacker successfully breached multiple Mexican government agencies, stealing 150 gigabytes of sensitive information that included 195 million taxpayer records, voter data, government employee credentials, and civil registry files. Continue reading
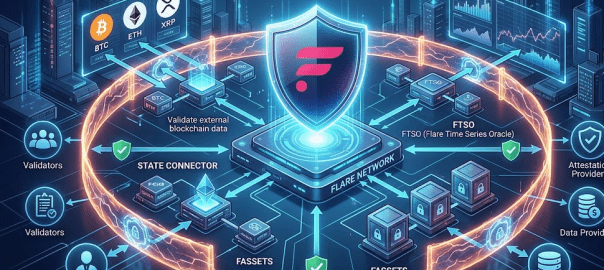
Beyond the Hype: 7 Hard Truths About Securing the Modern Decentralized Stack
The 2026 Crypto Compliance Mandate: Navigating MiCA and the End of the Grandfathering Era
28 Feb. 2026 /Mpelembe Media/ — The July 2026 Deadline and “Passporting” The European Union is fundamentally restructuring its digital asset market through the Markets in Crypto-Assets Regulation (MiCA). By July 1, 2026, the transitional “grandfathering” phase will permanently close, meaning any Crypto-Asset Service Provider (CASP) operating without full MiCA authorization will be doing so illegally. While some member states, like the Netherlands and Sweden, opted for much shorter transition periods that have already expired, the July 2026 date is the absolute maximum limit across the EU. Securing this license grants firms EU-wide “passporting” rights, allowing them to serve clients across all 27 member states with a single authorization. Continue reading
The Watchers Exposed: How a Single Platform Connects ChatGPT Selfies to Federal Intelligence Reports
Your Chatbot is Filing Reports to the Treasury: The Hidden Architecture of AI Surveillance
Securing the Cyberspace: The Impact of Zambia’s 2025 Cyber Laws on Security and Civil Liberties
Zambia’s Digital Vault: 6 Takeaways from the New Cybersecurity Revolution
Feb. 24, 2026 /Mpelembe Media/ –Zambia is currently undergoing a rapid digital transformation characterized by the expansion of financial technology (FinTech), increased internet penetration, and a concerted government push toward a digital economy. However, this growth has been accompanied by a surge in cyber threats, including massive financial fraud, online scams, and critical data breaches. In response, the Zambian government overhauled its legal framework by enacting the Cyber Security Act (2025) and the Cyber Crimes Act (2025). While the government champions these laws as necessary for national security and child online protection, civil society and digital rights advocates warn that the legislation grants the state sweeping surveillance powers, threatening freedom of expression, privacy, and democratic participation Continue reading
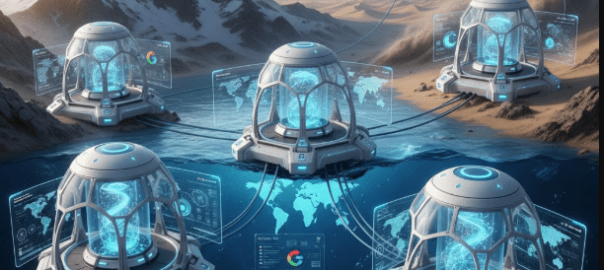
Full-Stack Visibility: Mastering the Architecture of Google Cloud Observability
10 Feb. 2026 /Mpelembe Media — Google Cloud Observability is a deeply integrated fabric of managed services designed to maintain reliability at a planetary scale. It moves beyond simple monitoring by correlating metrics, logs, traces, and profiles to provide a holistic view of infrastructure and application health. The platform is increasingly shifting toward open standards (OpenTelemetry, Prometheus) and AI-assisted operations (Gemini) to reduce the complexity of managing distributed systems. Continue reading
Sovereignty, AI, and the Struggle for Control in Modern Enterprise Networks
Jan. 29, 2026 /Mpelembe Media/ — This research by Arelion highlights that a vast majority of enterprise leaders experience significant anxiety over protecting sensitive information across complex third-party networks. Organizations face mounting hurdles involving encryption management, artificial intelligence risks, and the intricacies of data sovereignty. Ultimately, these sources emphasize that while security investments are increasing, many businesses still struggle to maintain regulatory compliance and total visibility over their digital infrastructure. Continue reading
Google and the Global Limits of Digital Erasure
Jan. 28, 2026 /Mpelembe Media/ — There is a high-profile legal dispute involving Google and the law firm Hogan Lovells regarding data privacy regulations in Europe. The core of the conflict centers on the “right to be forgotten,” a principle that allows individuals to request the removal of personal information from search results. European courts are currently attempting to balance the preservation of individual privacy with the public’s right to access information. These legal proceedings are viewed as a critical test for the future of digital data control and internet transparency. Ultimately, the outcome of these battles will define the boundaries of how personal history is managed by global tech companies. Continue reading
The Evolution of Digital Deception: How 2025 Scams Blended into Daily Online Life
Jan. 20, 2026 /PRNewswire/ — The Q4 2025 Gen Threat Report highlights a significant shift in cybercrime, where fraudulent advertisements and deepfake content have become the primary methods for targeting consumers. These findings indicate that attackers are increasingly exploiting trusted social media platforms like Facebook and YouTube to host fake online shops and deceptive investment schemes. Rather than using complex technical exploits, modern scams trick individuals into performing routine digital actions, such as clicking links or scanning QR codes, to compromise their data. The report also identifies GhostPairing attacks and a sharp rise in identity-related breaches as growing risks that bridge the gap between mobile and desktop devices. Ultimately, the data warns that malvertising has evolved into a sophisticated tool that allows threats to blend seamlessly into everyday internet browsing. Continue reading